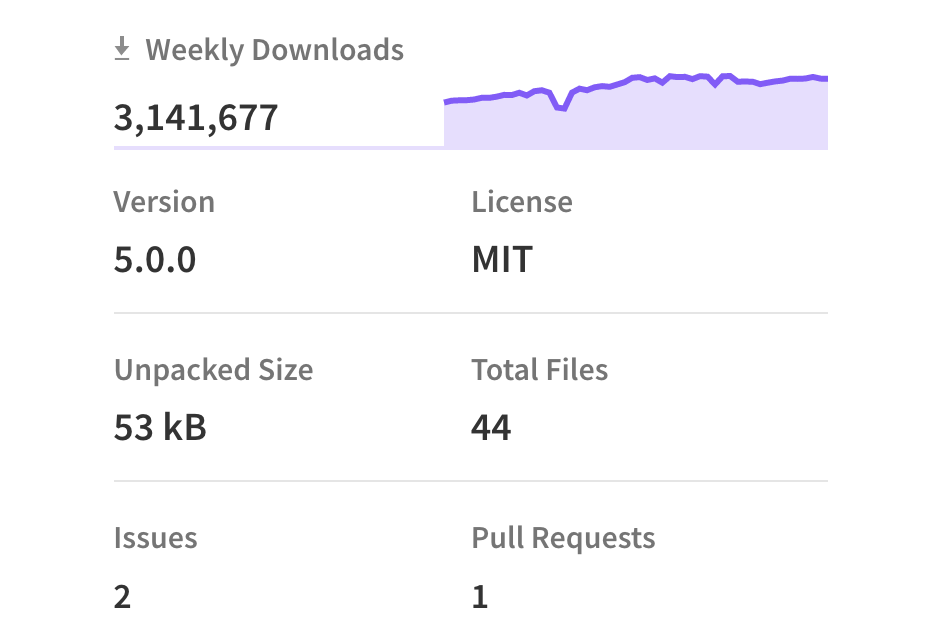
“pac-resolver” is a very popular NPM package, with over 3 million downloads per week and 285,000 public dependency repositories on GitHub. The developers of this package have recently released a patch to fix a vulnerability that could affect many Node.js applications with Remote Code Execution (RCE).
Developer Tim Perry disclosed a high-risk vulnerability in the pac-resolver dependency this week, noting that it could allow an attacker on the local network to remotely run malicious code in the Node.js process whenever an operator attempts to send an HTTP request. note.js is a well-known JavaScript runtime environment that can be used to run JavaScript-based web applications.
The vulnerability, with CVE ID CVE-2021-23406, relates to the way pac-resolver handles PAC files, which are PAC or Proxy-Auto Config files written in JavaScript to distribute complex proxy rules that instruct HTTP clients which proxy to use for a given host. These files are widely used in enterprise systems. They are distributed from local web servers and remote servers, usually via insecure HTTP distribution rather than HTTPS.
Although the PAC standard was originally introduced in 1996 as part of Netscape Navigator 2.0, it is still widely used in Amazon Web Services (CDK), Mailgun SDK and Google Firebase CLI.
It affects any developer who relies on Pac-Resolver version 5.0.0 in their Node.js applications prior to that time. The vulnerability affects your project if the developer has done the following three configurations.
- Explicitly use PAC files for proxy configuration
- Read and use the OS proxy configuration in Node.js on WPAD-enabled systems
- Use proxy configuration from any other untrusted source (environment variables, configuration files, remote configuration endpoints, command line arguments)
In either case, an attacker could configure a malicious PAC URL and remotely run arbitrary code on your computer when sending HTTP requests using the proxy configuration.
This vulnerability has now been fixed in pac-resolver v5.0.0. As pac-resolver is heavily downloaded and widely used in a variety of projects, this means that many developers of Node.js applications could be affected by this vulnerability and it is recommended that you double check your projects and ensure that you update to version 5.0.0 to fix the issue.