In early June, the widely used GNU C Library (glibc) released a patch to fix a relatively minor security vulnerability (CVE-2021-33574). Fixing the security issue should have been a good thing, but unfortunately this security patch introduced a new and more serious vulnerability (CVE-2021-38604).
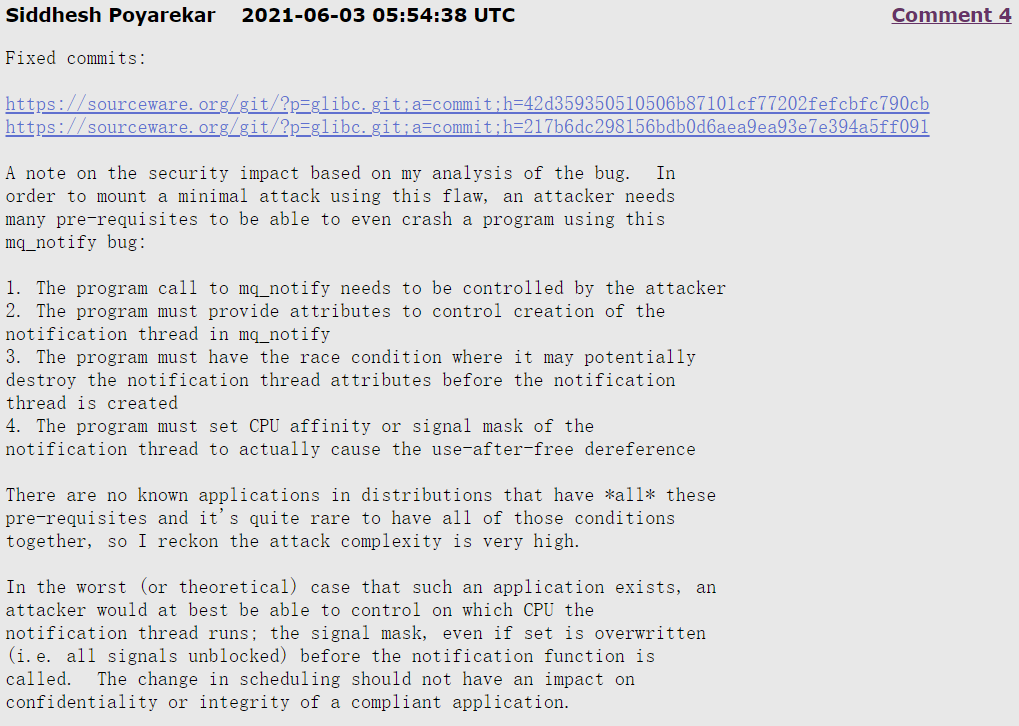
Siddhesh Poyarekar, a Red Hat software engineer, said that if an attacker wanted to exploit the initial security vulnerability to launch a minimal attack, he would need many prerequisites before he could exploit the vulnerability to crash the program. Nonetheless, since the security vulnerability was found it needs to be addressed.
However, after glibc was patched to fix this security vulnerability, it caused a more serious and easily exploited vulnerability. While checking for patches, Nikita Popov from the CloudLinux TuxCare team discovered that the new vulnerability could potentially cause a segmentation fault to be triggered within the library, which could cause any program using the glibc library to crash and create a denial of service (DoS) issue. More importantly, this vulnerability is more likely to be triggered than the old one.
RedHat gave this vulnerability a score of 7.5 in its Common Vulnerability Scoring System (CVSS), which is already a “high” score, meaning that an attack using this vulnerability is easy to build and does not require privileges.
This vulnerability was introduced by an upstream fix patch, specifically in the mq_notify.c file.
|
|
Nikita Popov discovered this problem while performing a “port of the security patch CVE-2021-33574 to a supported distribution’s routine” and found that null pointers could be passed in some cases.
According to Nikita Popov, glibc provides the main system primitives and is associated with most other Linux applications, including other language compilers and interpreters. It is the second most important component of the system after the kernel, so a problem with glibc could have a very large impact.
A patch for this vulnerability (CVE-2021-38604), and a fix for it, has been submitted to the glibc development team and has been integrated into the glibc library. In addition, a new test has been submitted to glibc’s automated test suite to detect this condition and prevent it from happening again in the future. glibc development team recommends that users upgrade to the latest stable version of glibc 2.34 or higher.